November/2022 New Braindump2go DEA-1TT5 Exam Dumps with PDF and VCE Free Updated Today! Following are some new Braindump2go DEA-1TT5 Real Exam Questions!
QUESTION 235
Refer to the Exhibit. What type of process, when performed on data, would produce the result shown?
A. Replication
B. Deduplication
C. Archive
D. Migration
Answer: A
QUESTION 236
Refer to the exhibit. Which operation is represented?
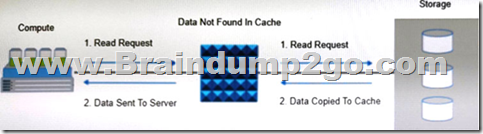
A. Write-through
B. Read Hit
C. Read Miss
D. Write-back
Answer: B
QUESTION 237
What is an accurate description about Dell EMC VxBlock system?
A. CI solution that combines compute, virtualization, network, software defined storage into an engineered solution.
B. HCI solution that combines compute, virtualization, network, software- defined storage into an engineered solution.
C. CI solution that combines compute, virtualization, network, storage into an engineered solution.
D. HCI solution that combines compute, virtualization, network, and storage optimized for VMware VSAN
Answer: D
QUESTION 238
An organization wants to consume compute, network, and storage resources through self-service portal.
Which cloud service model provides this capability?
A. Software as a Service
B. Infrastructure as a Service
C. Platform as a Service
D. Data as a Service
Answer: C
QUESTION 239
Which statement is true regarding virtual provisioning?
A. Shared and Thin LUNS can be expanded rapidly with only minor disruptions
B. Multiple shared storage pools can be created while each pool must be allocated to a unique thin LUN
C. Virtual provisioning enables more efficient allocation of storage to compute systems
D. Virtual provisioning prevents issues that arise from oversubscription
Answer: C
QUESTION 240
An organization is planning to secure the connection between the data center and cloud while performing data backup and replication.
Which security control mechanism will help organization to achieve the desired security?
A. ldentity and Access management
B. Intrusion Detection and Prevention
C. Firewall
D. Virtual Private Network
Answer: A
QUESTION 241
Which components should be used for interconnecting hosts to storage systems in FC SANs?
A. FC switches
FC hubs
FC N_Ports
B. FC switches
FC directors
FC E_Ports
C. FC directors
FC hubs
FC FL_Ports
D. FC switches
FC directors
FC FE_Ports
Answer: D
QUESTION 242
What is a key benefit for deploying a remote data protection and recovery solution in a data center environment?
A. Maximizes application and information availability
B. Reduces required maintenance time for IT resources
C. Avoids security risks that exposes the business data
D. Reduces the cost of protecting data
Answer: B
QUESTION 243
Which type of interface connects SSD drives to the storage array controller?
A. NVMe
B. NVMe/IB
C. NVMe-oF
D. NVMe/TCP
Answer: D
QUESTION 244
What is a feature of 5G technology?
A. Higher LAN bandwidth
B. Higher connectivity density
C. Higher WAN bandwidth
D. Higher transmission distances
Answer: C
QUESTION 245
What is the lowest to highest order of I/O performance among these storage devices?
A. SCM–> SSD –> DRAM–> SATA
B. SATA–> SSD–> SCM –> DRAM
C. SSD –> SCM–> SATA–> DRAM
D. DRAM–> SCM–> SSD-> SATA
Answer: C
QUESTION 246
What is an accurate statement about governance?
A. Creates the policies and enforces their adherence
B. Ensures removal of data security vulnerabilities
C. Determines strategy and operational rules by which companies are directed and managed
D. Restricts access privileges to certain legitimate users to avoid IT managed resource conflicts
Answer: C
QUESTION 247
Which Connectrix FC switch model supports NVMe in a 32Gb/s SAN fabric exclusively?
A. DS-6600B
B. MDS 9148S
C. DS-6505B
D. MDS-9132T
Answer: A
QUESTION 248
A company’s assets are continuously under attack.
To deploy a security control mechanism to protect these assets, what should be considered?
A. Minimize the work factor
B. Easy access to assets by authorized users
C. Limited access to assets by unauthorized users
D. Maximize the attack surface
Answer: B
QUESTION 249
What is a goal of cyber recovery?
A. Evaluate systems, networks, and applications to find vulnerabilities
B. Determine persistence access of system, networks, and applications
C. Abstract the physical compute hardware from the operating system and applications
D. lsolate copies of critical data to ensure that an uncompromised copy always exists
Answer: D
QUESTION 250
Refer to the exhibit. What type of NAS system(s) processes file write and read operations as described in the example?
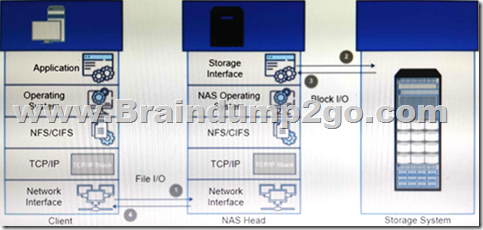
A. Scale-up and integrated NAS systems
B. Scale-up NAS system only
C. Scale -out NAS system
D. Integrated NAS system only
Answer: A
QUESTION 251
An organization is planning to adopt pre integrated systems to deploy compute, network, storage, and management functions as a single engineered solution.
Which approach should the organization adopt?
A. Service based approach
B. DIY approach
C. Vendor ready solutions
D. DCaaS solution
Answer: A
QUESTION 252
Why is it important to automate the operations management process in a data center environment?
A. converts CAPEX to OPEX
B. mitigates operation management risks
C. eliminates operational cost
D. ensures operational agility
Answer: B
QUESTION 253
An Ethernet switch has eight ports and all ports must be operational for 24 hours from Monday through Friday.
However, a failure of Port 7 occurs as follows:
Monday=4 PM to 11 PM
Wednesday= 2 PM to 10 PM
Friday= 5 AM to11 AM
What is the MTTR of Port 7?
A. 36 hours
B. 5 hours
C. 7 hours
D. 33 hours
Answer: C
QUESTION 254
A host sends one write /O to the RAID 1 array.
How many writes does it take for the array to store the data?
A. Six write 1/Os
B. Four write I/Os
C. Two write I/Os
D. One write I/Os
Answer: B
QUESTION 255
A company is using an intrusion detection and prevention system (IDPS) to scan and analyze intrusion events.
Which IDPS technique uses a database that contains known attack patterns?
A. Intrusion-based
B. Policy-based
C. Anomaly. based
D. Signature-based
Answer: C
QUESTION 256
Cloud tiering is the part of which tier?
A. Policy
B. Secondary Storage
C. Primary Storage
D. Application
Answer: D
QUESTION 257
What type of network connectivity is illustrated in the image below?
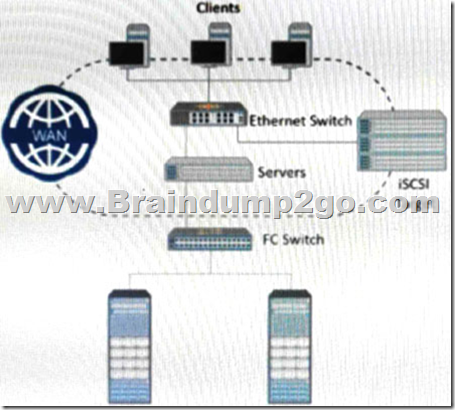
A. Compute to storage connectivity
B. Data center to data center connectivity
C. Storage to hybrid cloud connectivity
D. Compute to hybrid cloud connectivity
Answer: D
QUESTION 258
What is an accurate statement about Challenge Handshake Authentication Protocol (CHAP) control?
A. Enables initiators and targets to authenticate each other by using a shared secret code
B. Provides strong authentication for client-server applications by using secret-key cryptography
C. Allows a client to access protected resources from a resource server on behalf of a resource owner
D. Enables an organization to use authentication services from an identity provider
Answer: A
QUESTION 259
An IT organization wants to deploy four FC switches for compute and storage system connectivity. To meet performance requirements, a maximum of one active ISL and redundant ISLs for their compute to storage traffic.
Which FC SAN topology should be recommended?
A. Single switch
B. Partial mesh
C. Multi-switch
D. Full mesh
Answer: C
QUESTION 260
What is a purpose of the policy engine in a data archiving environment?
A. A Facilitates manual searching for archived data in archive storage
B. Moves the appropriate data into archive storage automatically
C. Automates the process of identifying the data to move from archive to primary storage
D. Enables manual migration of older archived data between archive storage devices
Answer: A
QUESTION 261
Which management monitoring parameter involves examining the amount of infrastructure resources used?
A. Configuration
B. Capacity
C. Performance
D. Availability
Answer: A
QUESTION 262
A Fibre Channel switch has eight ports and all ports must be operational from 6 AM to 6 PM, Monday through Friday.
However, a failure of Port 4 occurs with the week as follows:
Monday= 11 AM to 1 PM
Wednesday= 5 PM to 10 PM
Thursday= 7 AM to 10 AM
Saturday= 11 AM to 1 PM
What is the availability of Port 4 in that week?
A. 80%
B. 86.7%
C. 90%
D. 81 6%
Answer: B
QUESTION 263
What functionality does the control layer provide in a software-defined networking architecture?
A. Forwards data packets based on application layer requirements
B. Defines network behavior through physical network device policies
C. Establishes communication between the infrastructure and interface layers
D. Extracts network information from the data plane and sends it to the application layer
Answer: C
QUESTION 264
Which plane of the SDDC architecture provides a CL and GUI for IT to administrator the infrastructure and to configure policies?
A. Data plane
B. Management plane
C. Control plane
D. Service plane
Answer: B
QUESTION 265
What is a feature a hypervisor?
A. lsolates the physical resources of a single compute system
B. Provides a VMM that manages all VMS on a single compute system
C. lsolates the VMs on a single compute system
D. Provides a VMM that manages all VMs on a clustered compute system
Answer: A
QUESTION 266
A backup administrator has defined a backup policy. The policy requires full backups to be performed at 9 PM every Sunday and incremental backups performed at 9 PM the remaining days. If files were accidentally deleted Thursday morning, how many backup copies are required to restore the files?
A. 4
B. 5
C. 2
D. 3
Answer: C
QUESTION 267
What accurately describes the scale-out storage architecture?
A. Scales the capacity only within a single storage system.
B. Provides a fixed capacity ceiling that limits scalability beyond a storage system.
C. Provides the capability to maximize its capacity by adding nodes to the cluster.
D. Restricts scalability to the limits of the storage controllers.
Answer: C
QUESTION 268
Which network performance attribute is achieved when using flow control in FCIP?
A. IP network congestion detection and handling
B. Eliminate IP packet fragmentation
C. IP packet collision detection and handling
D. In-order packet delivery
Answer: A
QUESTION 269
Refer to the Exhibit. What type of FC port connects each FCIP gateway to each FC SAN?

A. EX_Port
B. VE_Port
C. E_Port
D. TE_Port
Answer: C
QUESTION 270
Which statement describes machine learning?
A. Organizes data efficiently so that compute systems can learn
B. Applies an algorithm to large amounts of data for pattern discovery
C. Developing a program to compute every possible outcome
D. Replicating a detailed process and then implementing it in software
Answer: D
QUESTION 271
Which functionality is provided by a process login in a Fibre Channel (FC) SAN environment?
A. Exchanges service relevant parameters between an N_port and an N_port
B. Establishes a connection to the fabric between an N_port and an F_port
C. Exchange ULP-related parameters between two N_ports
D. Establishes a session that occurs between two E_ports
Answer: C
QUESTION 272
Which type of data protection is used to move primary data to lower cost storage and helps to enforce compliance requirements?
A. Backup
B. Replication
C. Deduplication
D. Archive
Answer: C
QUESTION 273
A user lost access to a key VM due to a hardware failure. A proxy server regularly takes PIT snapshots of the VM to protect the data.
What type of data protection method is this called?
A. Agent-based
B. Image-based
C. Backup as a service
D. Local replication
Answer: C
QUESTION 274
Why is it important for organizations to store, protect, and manage their data?
A. To reduce the amount of data to be replicated, migrated, and backed up
B. To develop and deploy modern applications for business improvement
C. To eliminate complexity in managing the data center environment
D. To meet the requirements of legal and data governance regulations
Answer: D
QUESTION 275
What is a benefit of application virtualization?
A. Avoids conflicts between different versions of the same application
B. Enables an application to directly access a LUN on a storage system
C. Runs applications without requiring the use of cache memory
D. Presents more memory to an application than is physically available
Answer: A
QUESTION 276
Which set of factors govern the overall performance of a hard disk drive?
A. Seek time
Rotational latency
Bandwidth
B. Seek time
Rotational latency
RAID level
C. Seek time
Rotational latency
I/O operations per second
D. Seek time
Rotational latency
Data transfer rate
Answer: D
QUESTION 277
What is a function of the metadata service in an OSD storage system?
A. Generates the file system namespace from the data to be stored
B. Manages the file system storage space for all remote clients
C. Manages physical OSD containers on which data is stored
D. Generates an object ID from the data to be stored
Answer: C
QUESTION 278
Which modem technology enables data to be securely collected and processed at point of creation to create new value?
A. Big Data
B. Edge Computing
C. Private cloud
D. AI/ML
Answer: B
QUESTION 279
Which uses an orchestrated approval process to assist decision making using an agile methodology?
A. Security management
B. Performance management
C. Configuration management
D. Change management
Answer: C
QUESTION 280
What is a function of a continuous data protection (CDP) appliance?
A. Runs data protection software and manages replications within and across data centers
B. Stores all data that has changed from the time the replication session started
C. Migrates deduplicated data from the source volume to the target volume during replication
D. Intercepts writes to the production volume and splits each write into two copies
Answer: D
QUESTION 281
What is a benefit of application virtualization?
A. Avoids conflicts between different versions of the same application
B. Enables an application to directly access a LUN on a storage system
C. Runs applications without requiring the use of cache memory
D. Presents more memory to an application than is physically available
Answer: A
QUESTION 282
What is the goal of a business continuity solution?
A. Reduce the amount of investment in protecting an organization’s business-related data.
B. Avoid a disaster in a data protection environment to control the loss of data.
C. Ensure information availability that is required to conduct vital business operations.
D. Eliminate security threats in a data protection environment for continuous access to data.
Answer: C
Resources From:
1.2022 Latest Braindump2go DEA-1TT5 Exam Dumps (PDF & VCE) Free Share:
https://www.braindump2go.com/dea-1tt5.html
2.2022 Latest Braindump2go DEA-1TT5 PDF and DEA-1TT5 VCE Dumps Free Share:
https://drive.google.com/drive/folders/16-_wP5bdeQaxXUBkqQAjHEpBqMXlwPly?usp=sharing
3.2021 Free Braindump2go DEA-1TT5 Exam Questions Download:
https://www.braindump2go.com/free-online-pdf/DEA-1TT5-PDF-Dumps(236-282).pdf
Free Resources from Braindump2go,We Devoted to Helping You 100% Pass All Exams!





